Sophos specialister offentliggjorde en rapport, dedikeret til øget aktivitet af MegaCortex kryptograf.
Thans afpresser er hovedsageligt orienteret i erhvervslivet og bruges i de nøje planlagte målrettede angreb.Sådanne hændelser er en reel tendens i den seneste tid, og mange store virksomheder led af målrettede angreb: det er værd at huske LockerGoga "heroiske handlinger". Dens offer var en af verdens største aluminiumsproducenter Norsk Hydro, og en række store kemiske virksomheder.
Andre trusler, som lignende tilgang er Ryuk, BitPaymer, Dharma, SamSam og Matrix.
Det sagde Sophos-analytiker megacortex blev opdaget i januar 2019, når nogen uploadede malwares prøve på VirusTotal. Siden da er antallet af angreb konstant vokset: i alt eksperter noteret 76 hændelser, med 47 af dem (næsten to tredjedele) sket i den sidste uge.
MegaCortex-angreb påvirkede virksomheder i USA, Canada, Holland, Irland, Italien og Frankrig.
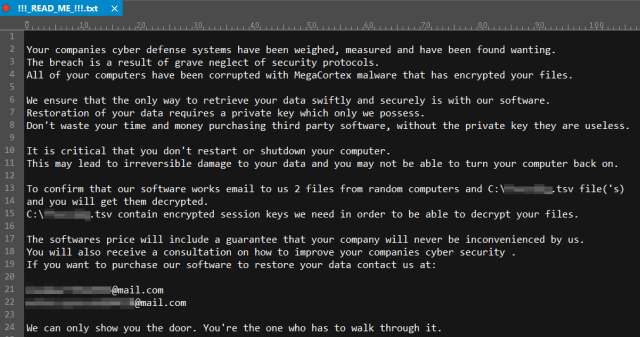
Kryptografers operatører forsøger så hurtigt som muligt at nå domænets controllere og sprede trusler på så mange systemer som muligt. "Recognize" MegaCortex skyldes kun afpressernes budskab, der kan ses nedenfor, eller ved at ændre filernes udvidelser, efterhånden som malware ændrer dem i en tilfældig rækkefølge af otte symboler.
I rapporten anerkender Sophos-forskere, at de ikke kunne opdage, hvordan afpresser kommer på inficerede værter. I sin side, IT-eksperter skriver i sociale netværk, at MegaCortex angiveligt bruger til det Rietpoof uploader. Dette er ret interessant observation, da kryptografer normalt kommer i netværk gennem brutforcen af de dårligt beskyttede RDP-endepunkter eller som en nyttelast af anden fase af angrebet, lige efter infektion af maskiner med intimidere eller Trickbot Malware.
Da angrebet synes at indikere, at en administrativ adgangskode blev misbrugt af de kriminelle, vi anbefaler også den udbredte anvendelse af tofaktorautentificering for alt, der i øjeblikket kun kræver en adgangskode, og kan bruge 2FA.
At opbevare regelmæssige sikkerhedskopier af dine vigtigste og mest aktuelle data på en offline lagringsenhed er den bedste måde at undgå at skulle betale en løsesum helt.
Kilde: https://news.sophos.com
