
ZDNet journalister pegede opmærksomhed på usædvanlige problem med Git-repositories, herunder GitHub, Bitbucket og GitLab brugere.
Last week unknown attacker or a group of attackers started hacking other people’s repository, slette alle indledende koder og kommentarer, og senere kræve buyout til data recovery.Besked med buyout anmodning, der er præsenteret ovenfor,, also says that prior to deleting information attacker thoughtfully saved it on his server, and victim has 10 days on payment transition. Otherwise attacker threatens to delete data forever.
To recover your lost code and avoid leaking it: Send us 0.1 Bitcoin (BTC) to our Bitcoin address ES14c7qLb5CYhLMUekctxLgc1FV2Ti9DA and contact us by Email at admin@gitsbackup.com with your Git login and a Proof of Payment. If you are unsure if we have your data, contact us and we will send you a proof. Your code is downloaded and backed up on our servers. If we don’t receive your payment in the next 10 dage, we will make your code public or use them otherwise, , — says blackmailer’s message.
Currently on Bitcoin-wallet that is mentioned in the message was not received any transactions, though journalists inform about 392 ofre of the blackmail campaign on GitHub only while Atlassian company experts say about at least 1000 involved users.
Ifølge Dårlige pakker company specialists, the most likeable is that this attack was planned, and hackers scanned network, searching for /.git/config and files with Git configuration, and later used found accounts for penetration repositories. In the interview to ZDNet, GitLab specialists confirmed that this expert’s theory is trustworth, and in the case that investigated GitLlab, issue was hidden in compromised accounts that were stored in the open search.
It is worth noting that StackExchanges users consider that attackers does not delete information from their repositories, but just changes Git commits headlines. If this is true, data can be restored without buyout payments. On StackExchange have already prepared instruction for this case.
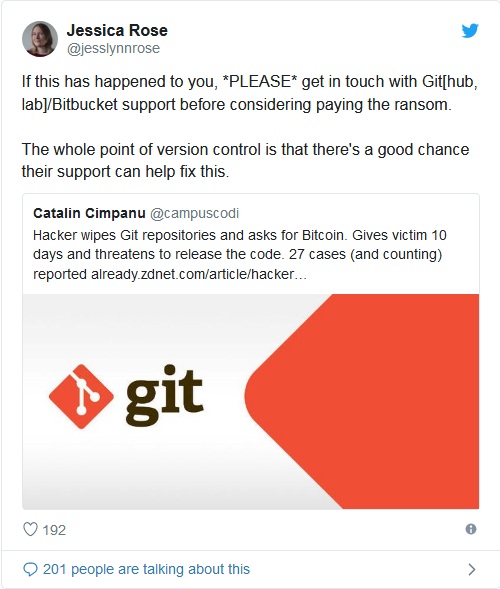
Desuden, security specialists actively call victims not to pay to the blackmailer and instead to turn in GitHub, GitLab and Bitbucket support that can allegedly help them.
Kilde: https://www.zdnet.com
