
Gaming series of motherboards from ASUS, a well-known Republic of Gamers (ROG) product line appears to have a vulnerability. This security breach is critical and worth your attention since it is extremely easy to exploit. Exactly, this breach is related not to exact motherboards, but to the complementary software – Armoury Crate.
Hacking the Armoury Crate
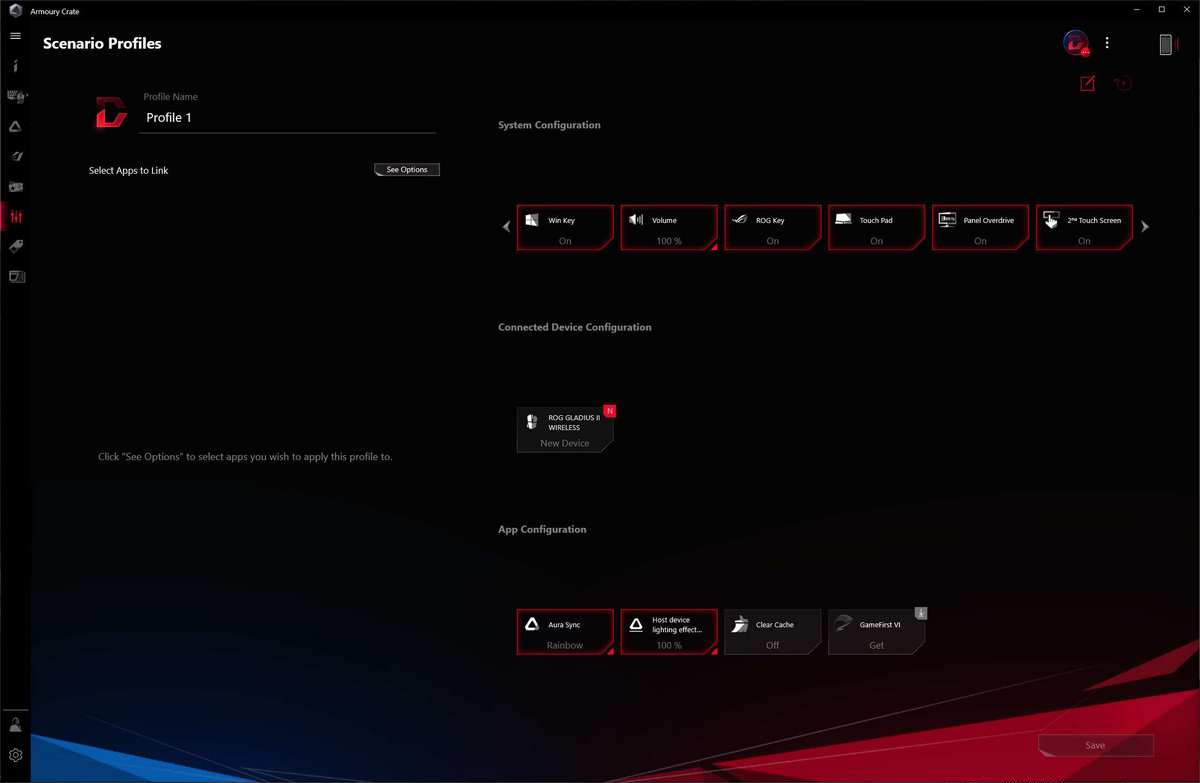
Armoury Crate is a program created by ASUS specially for the users of the motherboards of the ROG series. That app allows you to control all elements of your PC that are placed on the motherboard. Adjusting the CPU clock rate, fan speed or RAM frequency – all these things are possible through the graphic interface. This tool is very useful and loved by ASUS ROG users, but no one expected such a threat.
To manage the setups of low-level hardware, Armoury Crate uses a Lite Service. This is system process that is created together with the program installation. It is responsible for the correct interaction of the exact application with system components. It also works with a DLL that is needed for the correct operation of that tool. The path to this DLL is %PROGRAMDATA%\ASUS\GamingCenterLib. Since the program works on a very deep level, the privileges that this program uses are very high. Touching the Ring 2 or even Ring 1 is not a thing that must be done recklessly.
Where it hides?
The problem hides in the fact that Armoury Crate does not check the correctness of the DLL it uses. Anything can just swap it on the other library, and it will be executed with very high privileges. Fortunately, this security breach was not used by cybercriminals – it was just discovered by a bug-hunter. As he says, it is very easy to create a separate user with administrator privileges and then manage the system remotely.
As the same bug-hunter says, the privileges of the simple user are enough to inject the malicious DLL instead of a regular one. However, it can only be executed under the user with administrator privileges. Nonetheless, it is still a pretty often scenario when the computer is shared, for example, between younger and older children, with user and administrator privileges correspondingly. Once your elder brother is logged into the system, the malware is able to do what it is designed to do.
ASUS responds to the threat
The company was grateful to the bug-hunter for finding such a simply exploitable vulnerability. In an extremely short period of time – in only 18 days from the report date – the patch which fixes that breach will be available. Users are already waiting for October 1, 2021, because this breach is a perfect way of injecting something much more serious than adware or browser hijacker.
ASUS did not comment on this situation, besides promising to fix the problem. However, some further comments appeared from the aforementioned bug-hunter – AppTortellini. He says that such a situation is not something rare, especially when it comes to narrow-specification programs. In the case of Armoury Crate, they left this breach unsecured because it was likely concentrated on providing the main functionality and design of the app.
The exploit is already listed on the CVE website under the code “CVE-2021-40981”. Regardless of the fact that ASUS reacted pretty fast to that problem, there will be a lot of users who will miss it, or decide to install a patch later. Will it cause a spike of malware injection through that way? No one knows. But even antiviruses can be ineffective: gamers have a habit to disable the security tools from running into the background. That is done to save several gigabytes of RAM for the peak performance in games, but will you play games when your system is compromised?
